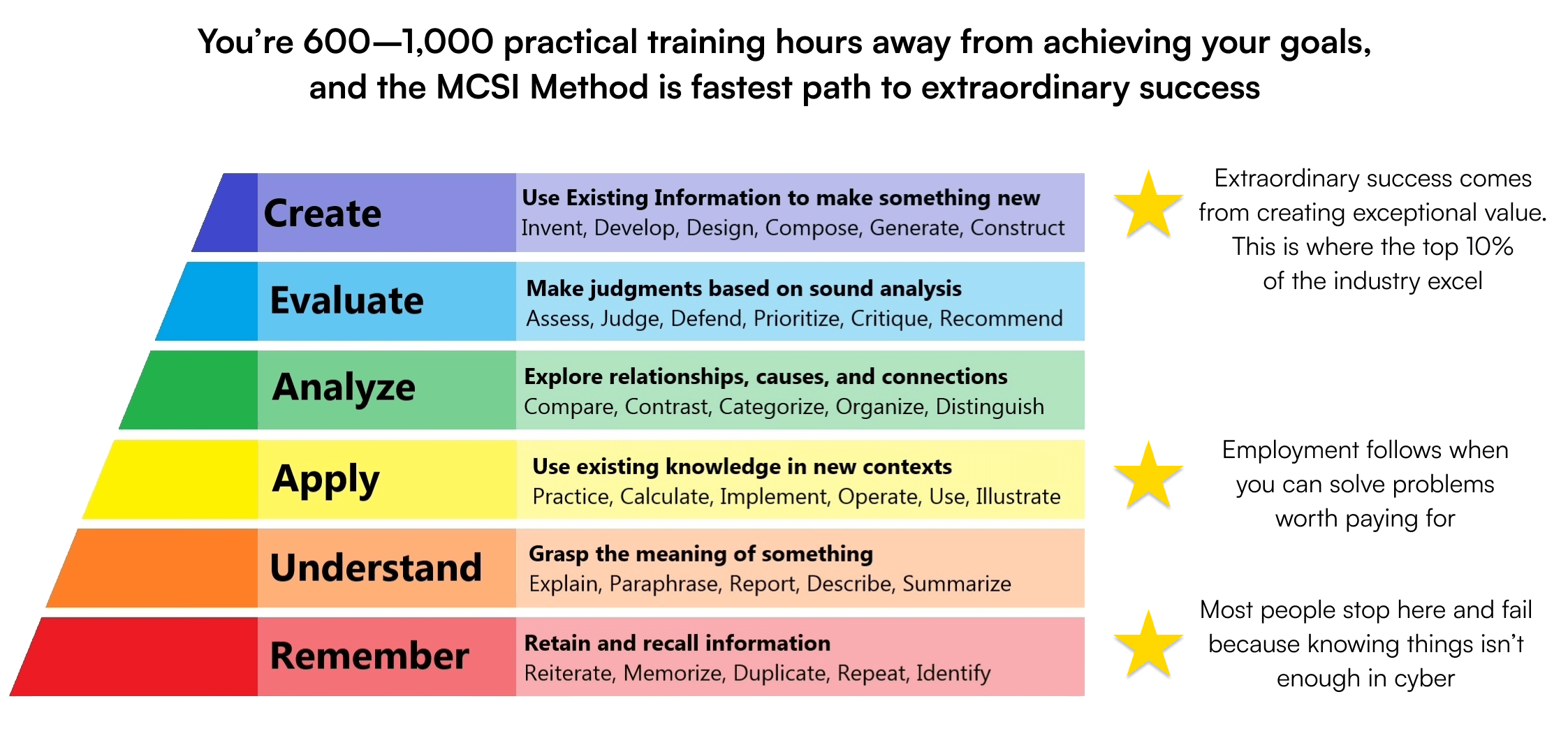
MCSI Bootcamps are high-quality training exercises created by seasoned professionals to help beginners learn vital cyber security skills faster. Our bootcamps have an established track record of achievement, with a high-rate of graduation success.
If you are seeking practical cyber training that will accelerate your career, our bootcamps are the perfect solution.
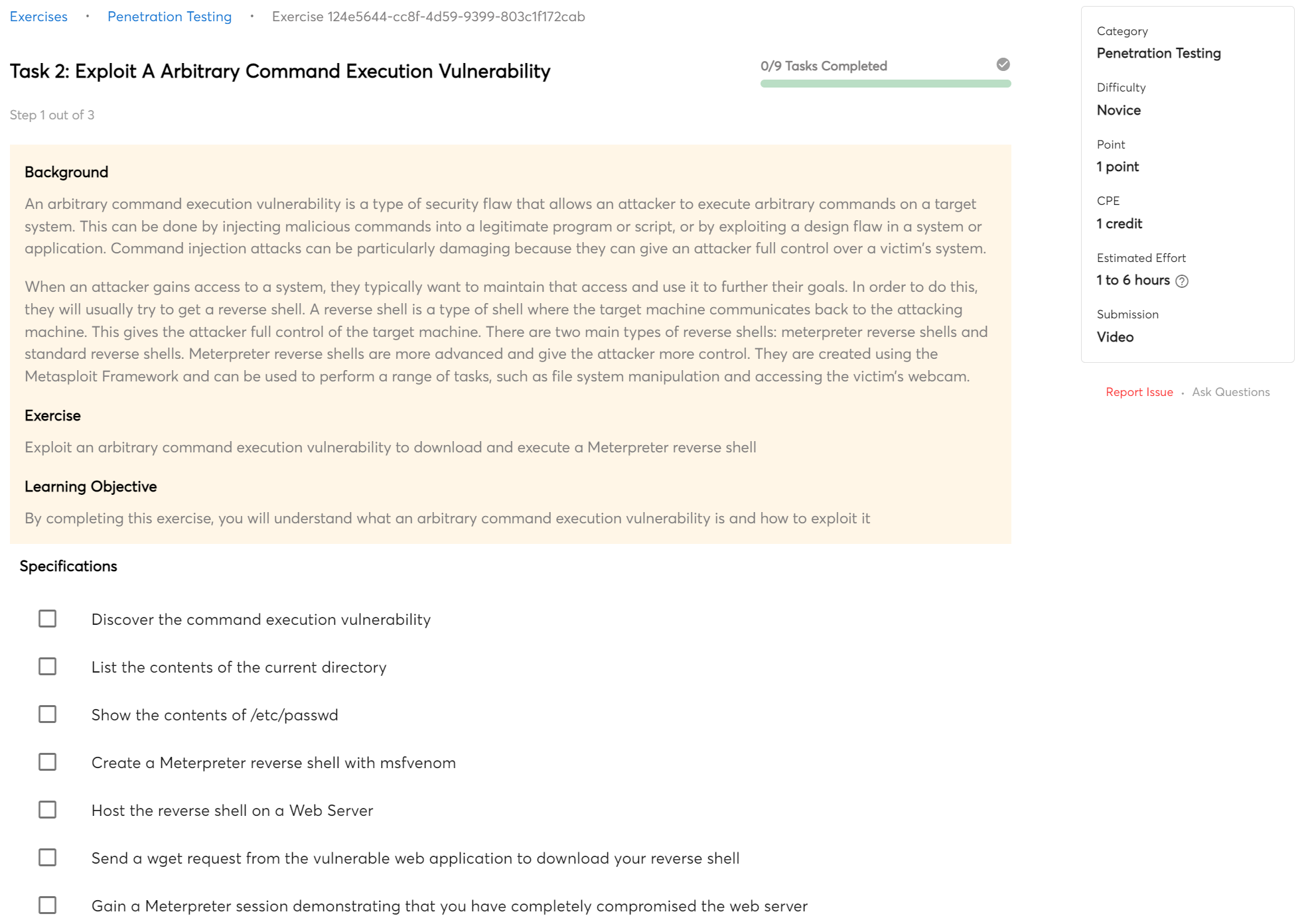
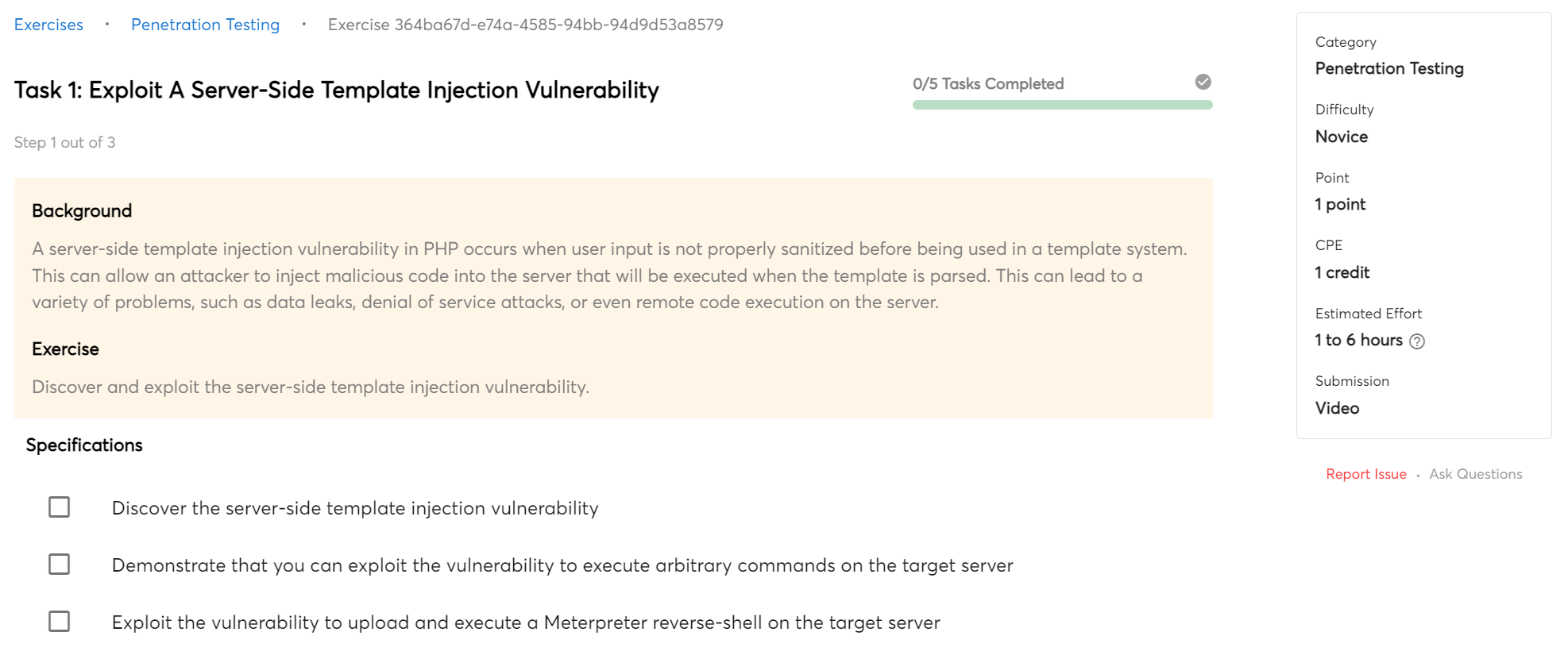
Sample Exercises
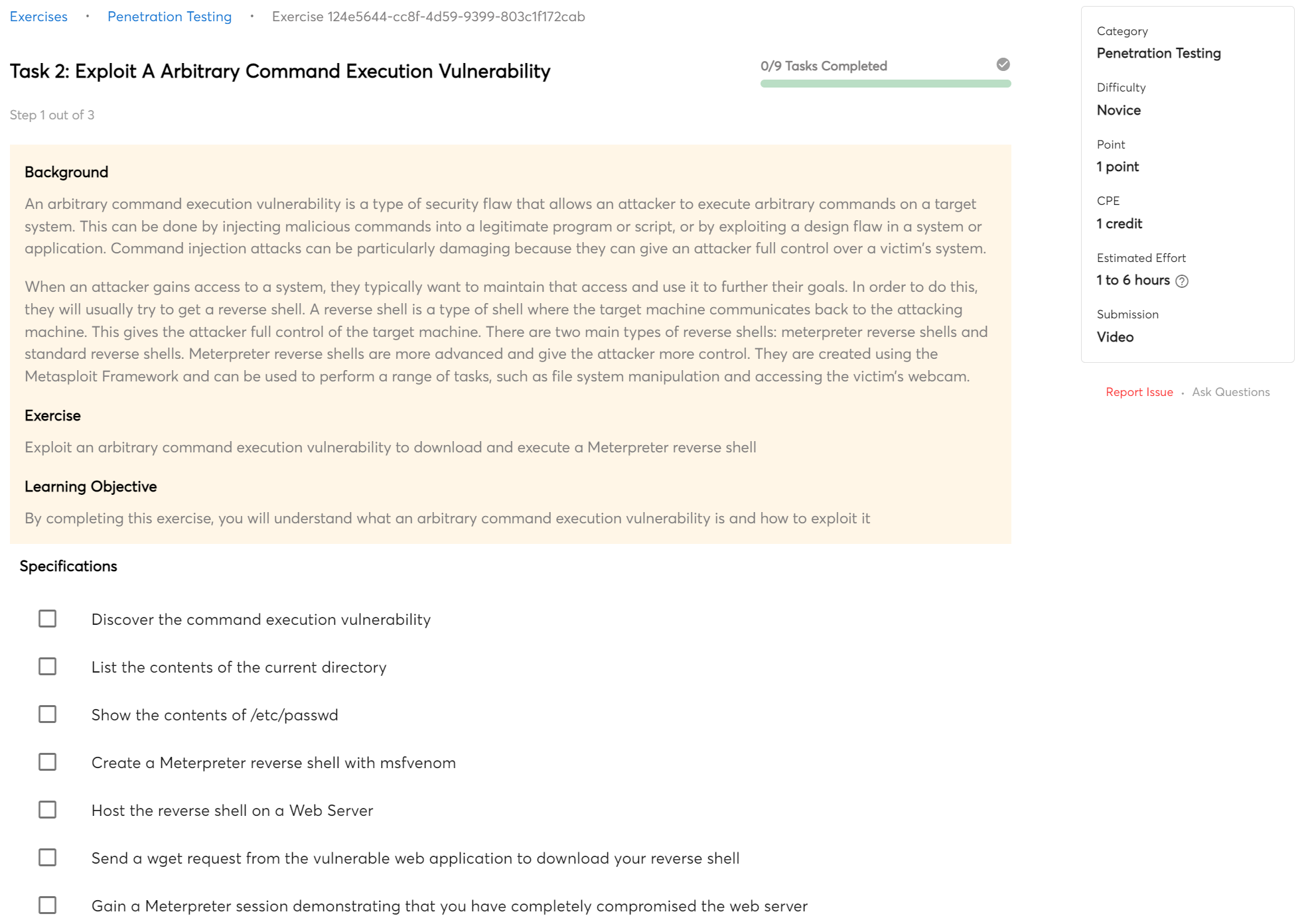
Exploit A Arbitrary Command Execution Vulnerability
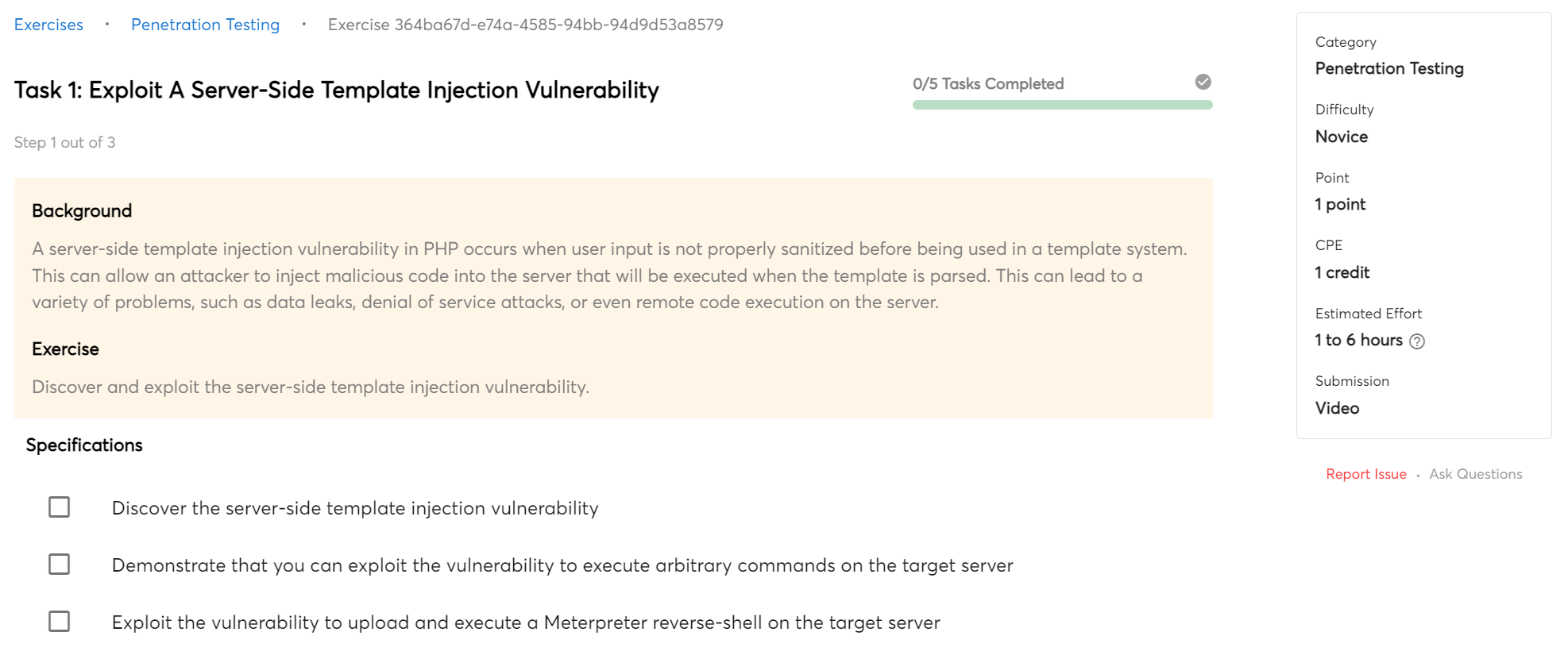
Exploit A Server-Side Template Injection Vulnerability
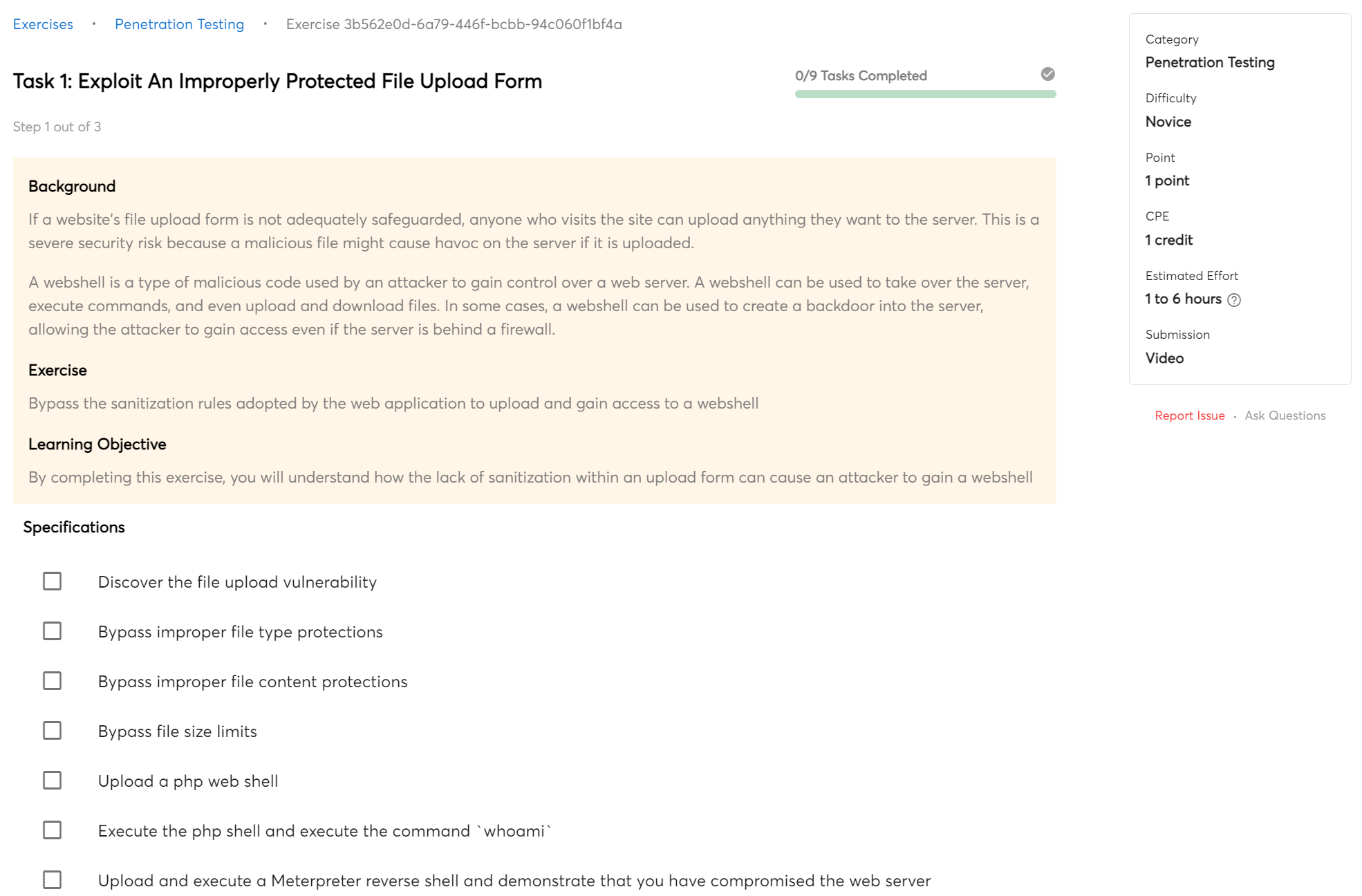
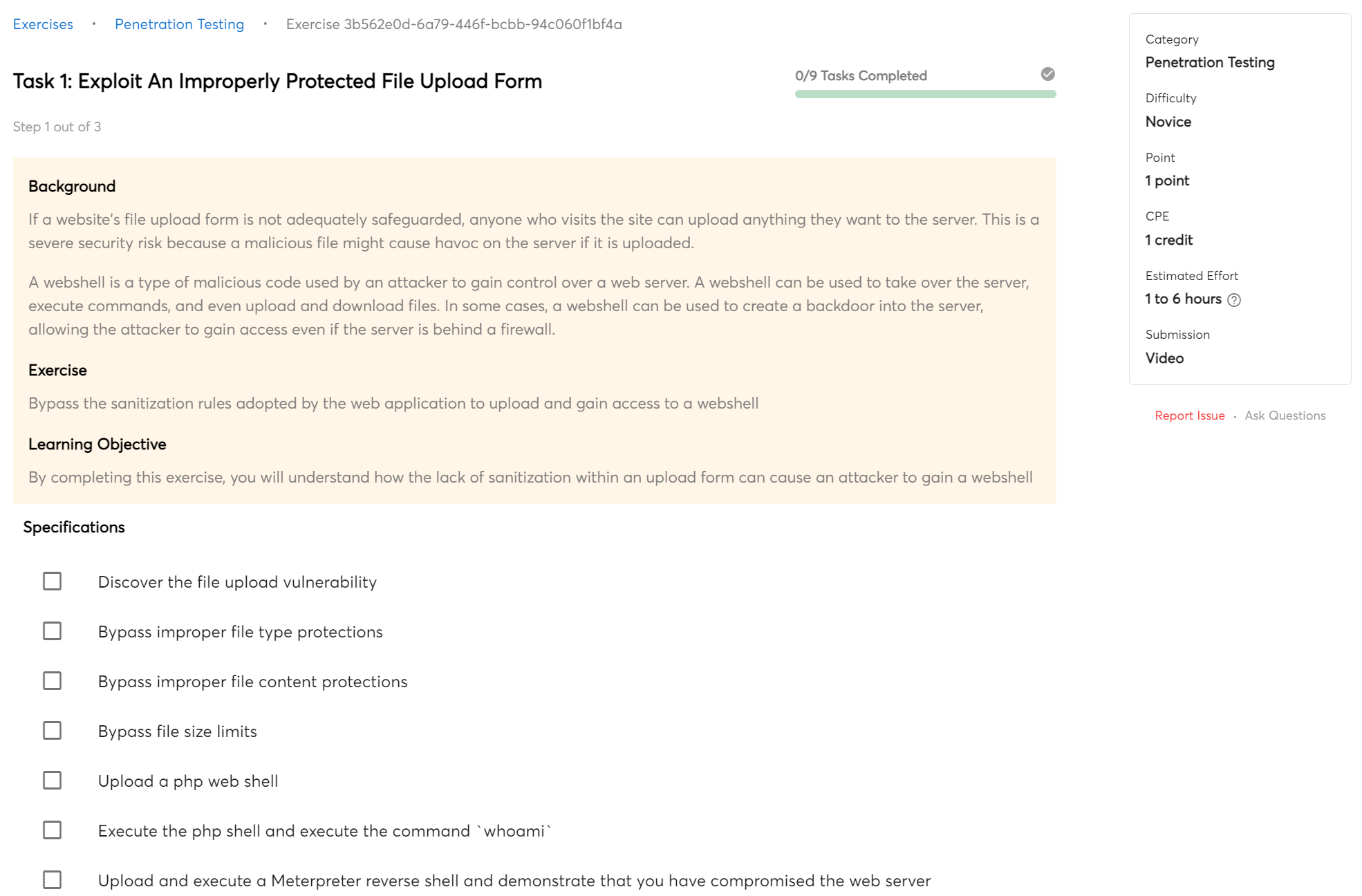
Exploit An Improperly Protected File Upload Form
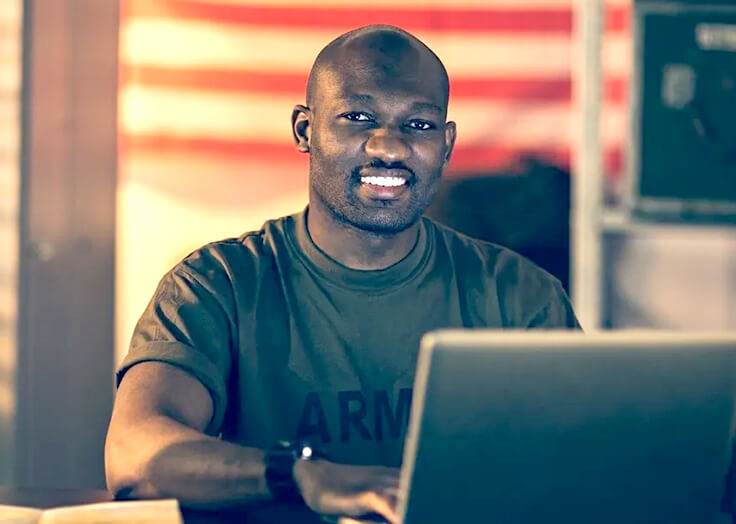
Our Instructors
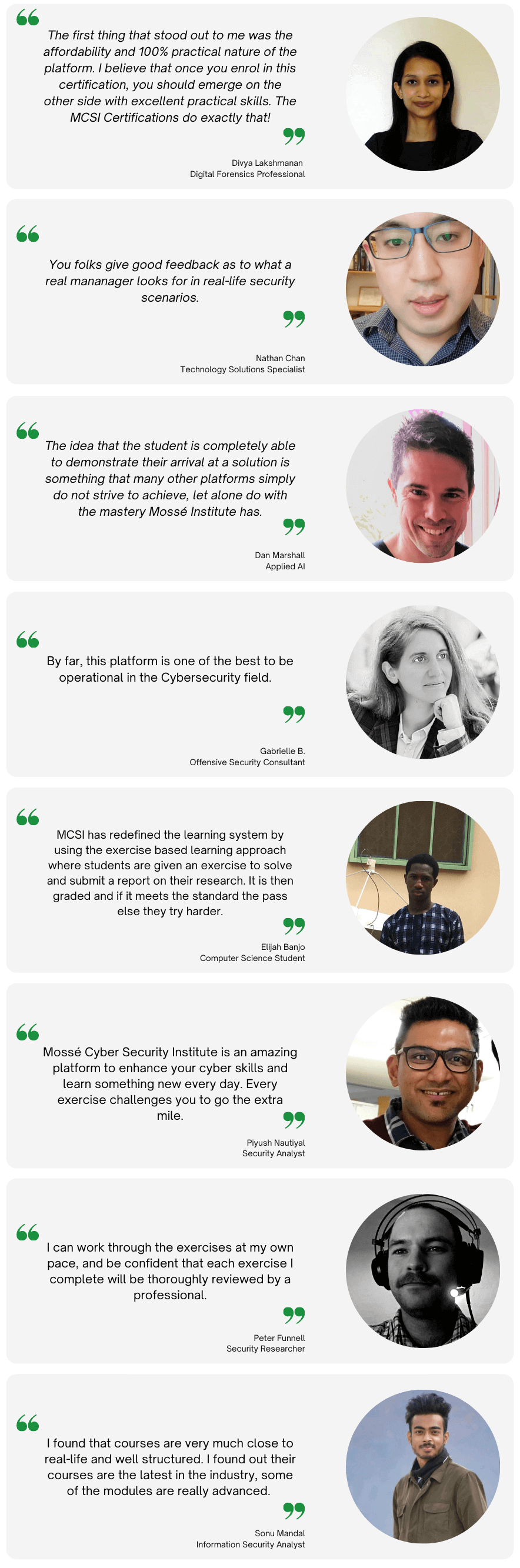
Student exercises are reviewed and graded by multiple instructors. This one-of-a-kind approach allows you to get highly personalized input from a number of successful professionals.
MCSI's teachers bring real-world experience and knowledge to the classroom, ensuring that students have the skills they need to excel in the field of information security. Due to their extensive experience in penetration testing, vulnerability assessment, reverse engineering, incident response, digital forensics, and exploit development, students will understand the most up-to-date defensive and offensive cybersecurity strategies and procedures.
Our instructors are passionate about information security and are always looking to further their own knowledge. Students who attend an MCSI course can be confident that they are learning from some of the best in the business. They can adapt their teaching approaches to match the demands of any student, regardless of their degree of expertise.
The MCSI team strives to provide the most comprehensive and up-to-date cybersecurity training available. Whether you are a seasoned security professional or new to the field, MCSI has a course that will meet your needs.
Receive personalized feedback from cybersecurity experts:
-
Overcome challenges and hurdles preventing you from advancing your skills
-
Receive guidance on how to focus your training efforts and avoid wasting time
-
Learn how to meet the industry's quality standards and produce high-quality work
-
When you're stuck, go to a support forum or ask inquiries to the instructors right on the platform
Help and Support
24/7 Discord Community
If you're looking for additional support during your studies, consider joining our Discord server. Our community of fellow students and instructors is always available to provide help and answer any questions you may have.
Personalized Support
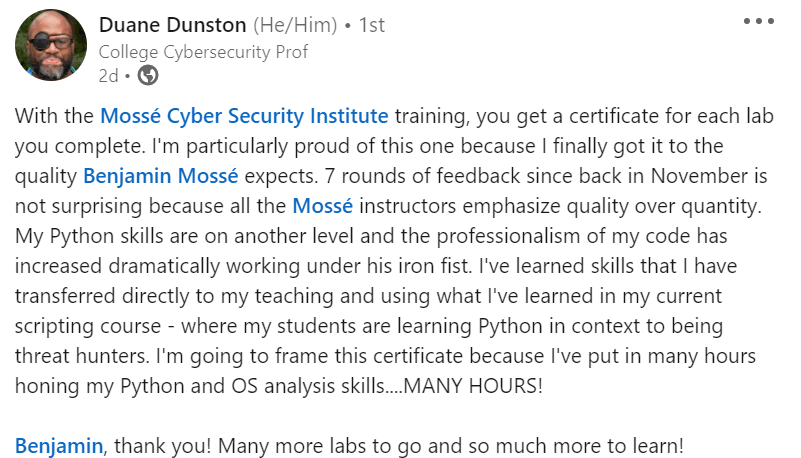
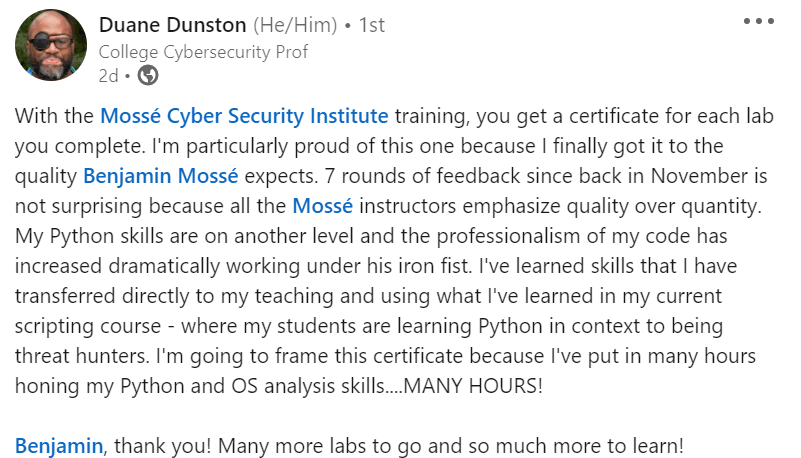
Your submissions will be reviewed by MCSI instructors, who will provide you with personalized feedback. This input is critical since it can assist you in identifying the areas where you need to enhance your skills. The instructor's feedback will also tell you how well you did an exercise and what you can do to improve your performance even further.
Click here to see an example of personalized feedback.
Our personalized support will take your skills to the next level. Read what a student says about it:
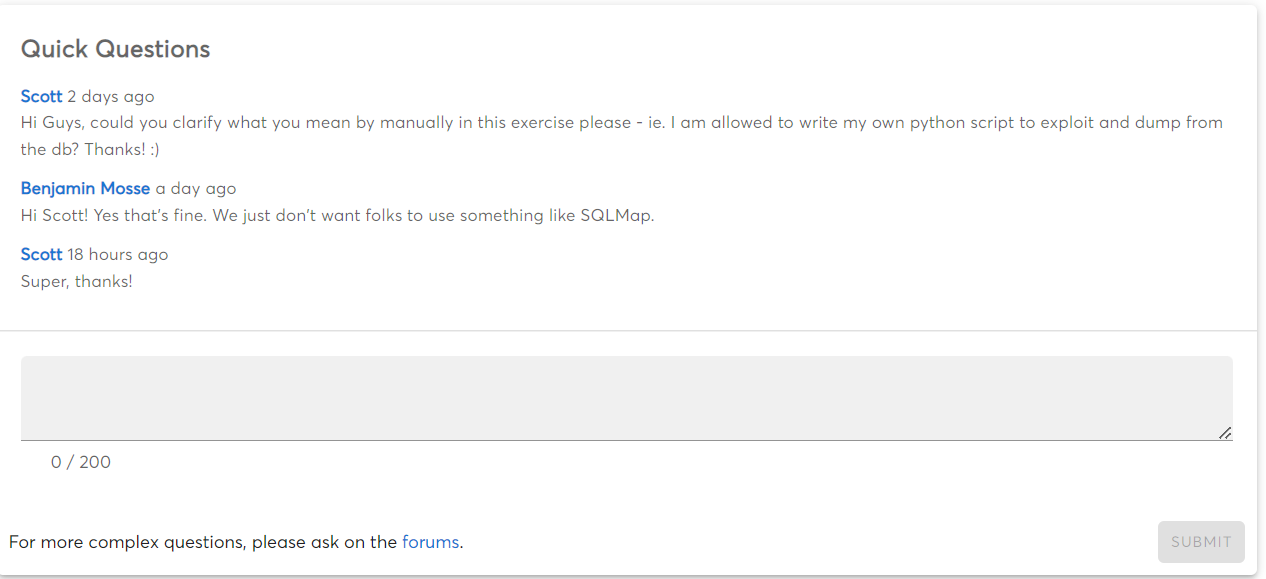
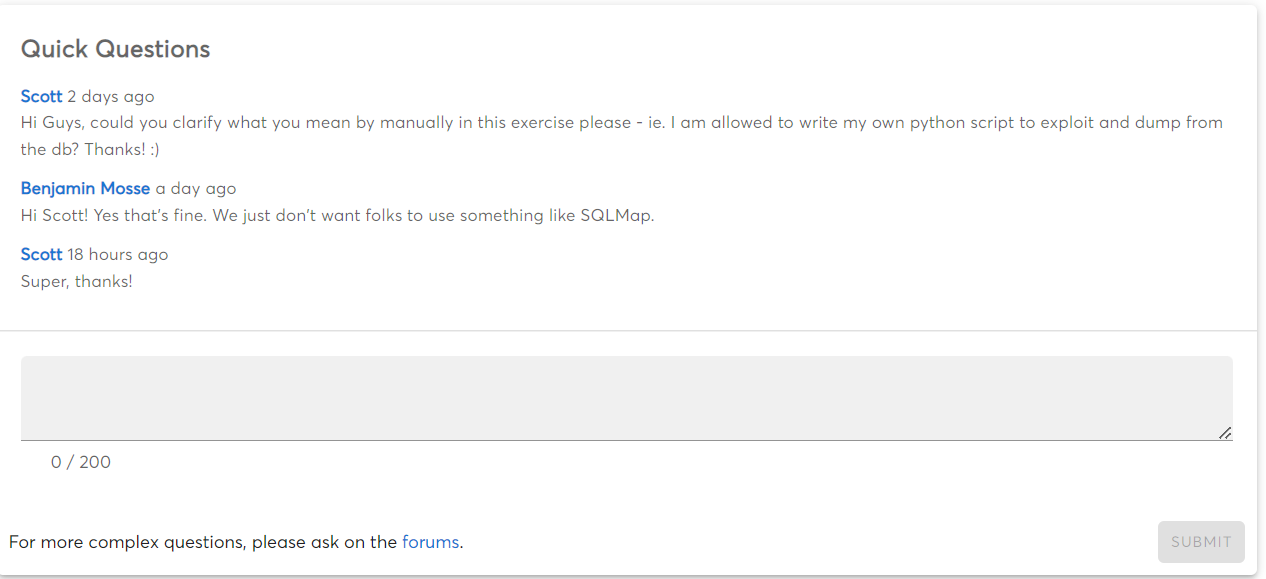
Quick Questions
If you have any questions or need clarification on any of the exercises, MCSI offers a Quick Questions section on each exercise where you can ask for help. This is a great resource to use if you need assistance. This feature is only available for paid courses.
Actively Maintained Course
This course is actively maintained to ensure that it is current and error-free. We want to ensure that you have the best possible experience while taking this course, which includes having access to accurate and current information. This course is also tested for flaws on a regular basis, so you can be sure you're getting a high-quality product.
This course is constantly updated with the support of trustworthy industry peers to ensure that students are acquiring the most up-to-date information and skills. This dedication to staying ahead of the curve is what distinguishes this course as one of the greatest in the market.
Prerequisites
Proficiency in the English language
You must have the ability to comfortably read and understand IT documentation written in English. Ideally, they have an IELTS score of 6.5 with no band less than 6 (or equivalent).
Note: You can register for this course without having undertaken an English test.
Training Laptop Requirement
This course can be completed on a standard training laptop. To ensure you have the necessary hardware to complete the course, your machine should meet the following specifications:
-
64-bit Intel i5/i7 2.0+ GHz processor or equivalent
-
8GB of RAM
-
Ability to run at least (1) virtual machine using Virtual Box, or an equivalent virtualization software
-
Windows 10 or later, macOS 10 or later, or Linux
-
Local administrator privileges
Do you support older operating systems?
Yes. Many of the exercises can be completed on older OS versions. A few of our students are successfully using older equipment to learn cyber security.
Knowledge Requirements
-
Knowledge of computer networking concepts and protocols, and network security methodologies
-
Knowledge of cyber threats and vulnerabilities
-
Knowledge of strategies and tools for target research
-
Knowledge of website types, administration, functions, and content management system (CMS)
-
Knowledge of scripting
Technical Requirements
-
Ability to deploy and configure virtual machines
-
Ability to deploy a Docker container
-
Ability to install software utilities and use command line tools
-
Skill in interpreting compiled and interpretive programming languages
Lab Environment
This course teaches you how to setup and configure your own cybersecurity lab.
There are numerous advantages to creating your own cybersecurity lab rather than paying for one. The cost savings are perhaps the most evident benefit. When compared to the expense of licensing a pre-built lab, creating your own lab can save you thousands of dollars. You also have the option of customizing the lab environment to meet your specific requirements. You can, for example, select the hardware and software that will be used in your lab.
Another advantage of setting up your own cybersecurity lab is that it allows you to learn new skills. Building a lab from the ground up necessitates knowledge of networking, system administration, and other technical subjects. This experience is invaluable in your career as a cybersecurity professional.
We frequently see students who can complete a task in a pre-built lab but cannot complete the same task at work. This is because these labs are meant to lessen work complexity, thereby creating an illusion of personal capabilities. It's also worth noting that you'll be expected to set up your own lab to test tools and techniques in the workplace. Employers may give you the resources to set up virtual computers and networks, but it will be up to you to manage the lab environment and maintain your tools.
Finally, you should know that pre-built labs are not commonly licensed by top cybersecurity professionals. They've realized that setting up a lab is simple, efficient, adaptable, cost-effective, and that it sparks creativity. It also nullifies risk of performing unauthorized actions against systems provisioned by a third-party.

 Beginner
Beginner