Everything you need to learn how to use the most popular cyber security tools in the field
MCSI’s `Security Tools Master Bundle` teaches how to use popular cybersecurity tools. The practical exercises teach how to leverage different tools in different cybersecurity roles. Throughout the bundle, we look at tools including:
The `Security Tools Master Bundle` unlocks all the Security Tools exercises MCSI offers. There is no time limit for this training. It is completely self-paced and there are no pre-requisites required.
By completing this bundle, you will know how to use popular cybersecurity tools. The skills you learn can be immediately applied in the field, or help you prepare for any I.T or cyber security job.
Fees
US$199 (+ GST if you're based in Australia).
Practical exercises must be completed online using MCSI's Online Learning Platform.
Terms and Conditions
Cooling-Off Policy
Receive a full refund if you change your mind about a purchase within 24 hours. No questions asked.
How to enrol
- Login/Register for MCSI's Online Learning Platform
- Select `Shop` from the left-side menu
- Find the Cyber Security Tools Specialist Bundle, select `Buy` and proceed through the checkout process. You can purchase using a Credit Card or PayPal
- Once you have enrolled in the Cyber Security Tools Specialist Bundle, the curriculum unlocks immediately
- In the left-side menu of the platform, select `Training & Education` then `MCSI Bundles`, and you will see the Cyber Security Tools Specialist Bundle listed
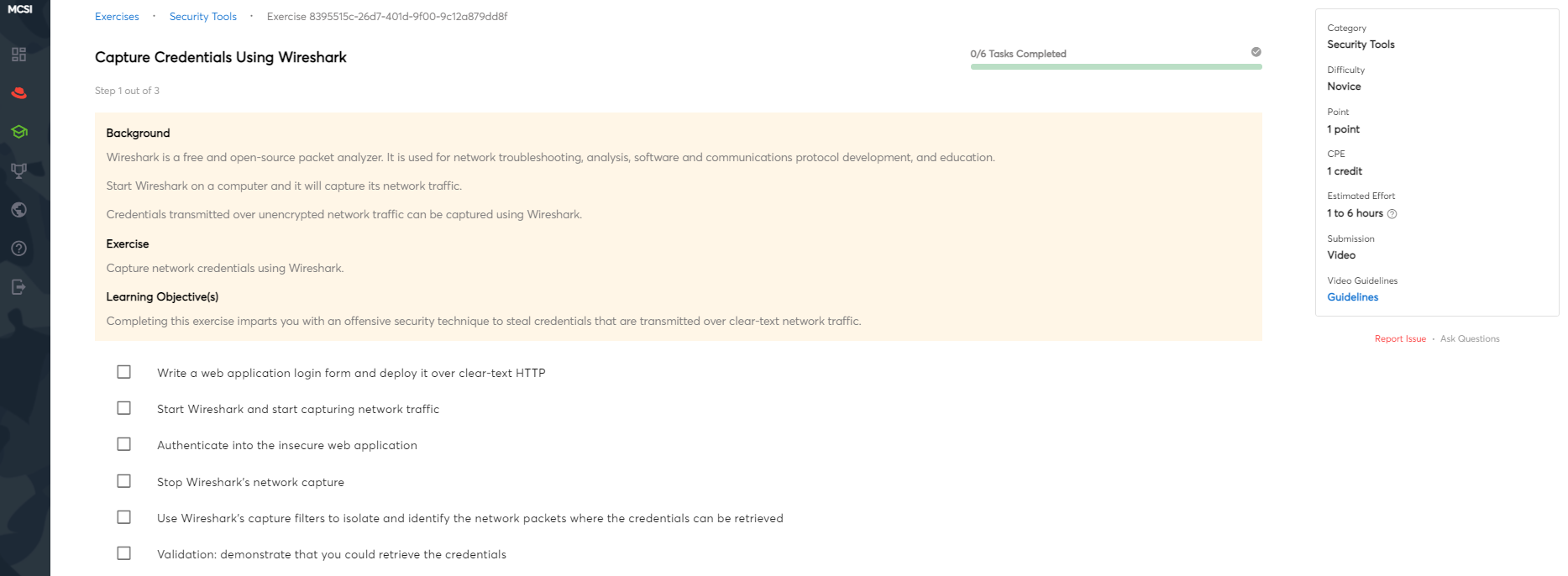
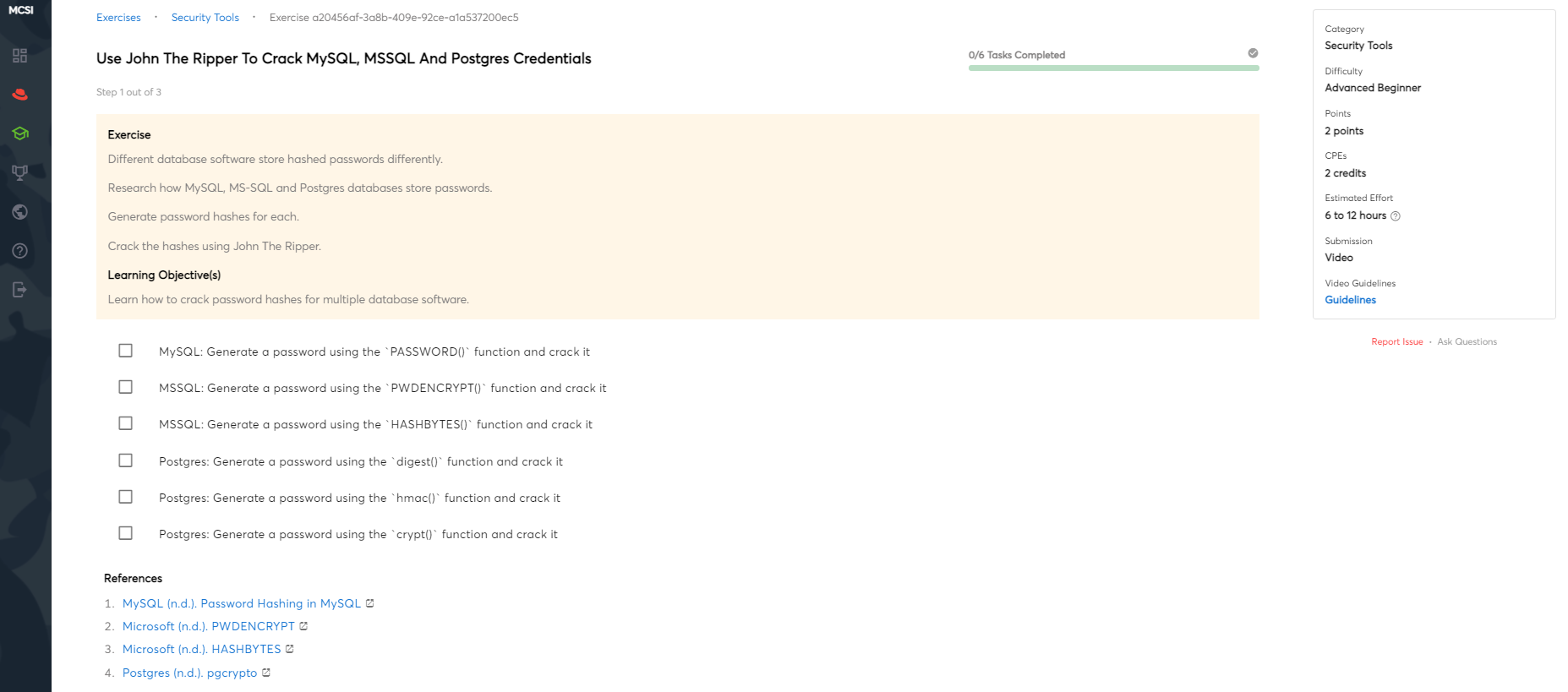
Sample Exercises
Below are three (3) exercises from the 30 exercises available in Metasploit Specialist Bundle:
Capture Credentials Using Wireshark (Novice)
Use John The Ripper To Crack MySQL, MSSQL and Postgres Credentials (Advanced Beginner)
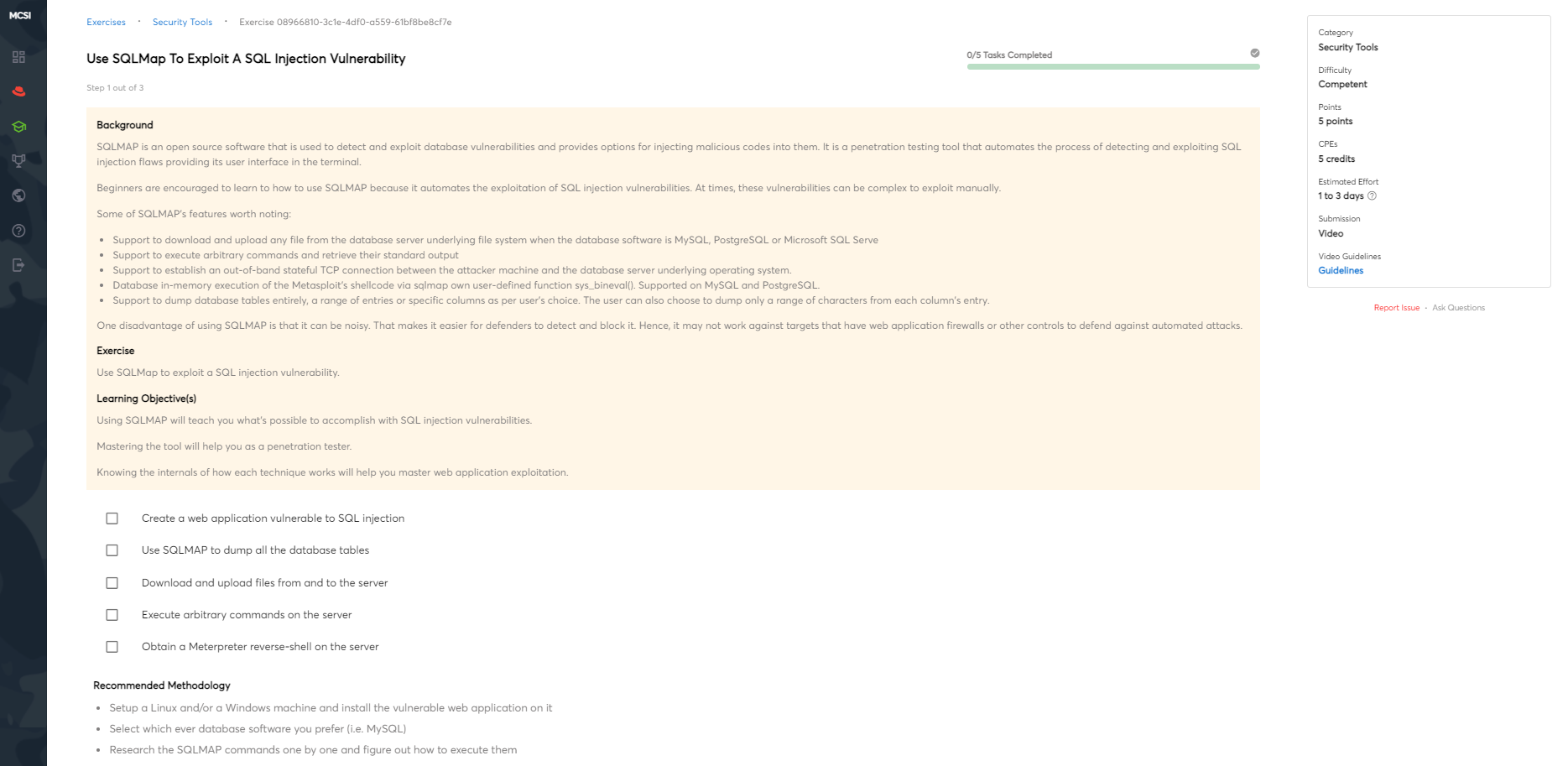
Use SQLMap To Exploit A SQL Injection Vulnerability (Competent)